A single compromised social media account can destroy a cryptocurrency project’s reputation, drain followers’ wallets, and trigger a price collapse in hours. The attack vectors are well understood, the defenses exist, and yet crypto projects — from small DeFi protocols to major exchanges — continue to lose control of their official accounts to hackers.
This guide explains how these attacks work, documents the most significant real-world incidents, and provides a comprehensive security checklist for any individual or organization managing crypto-related social media accounts in 2026.
Why Crypto Social Media Accounts Are Prime Targets
Cryptocurrency social media accounts are uniquely valuable to attackers for several interconnected reasons:
Trust is the product. Crypto projects often have no physical presence, no regulatory backing, and no customer service phone number. Their official social media accounts are frequently the primary signal that followers use to verify authenticity, track updates, and receive wallet addresses. A compromised official account can instantly direct thousands of followers to fraudulent links with a legitimacy that no independent scammer can manufacture.
The attack window is narrow and profitable. The window between a successful account takeover and account recovery is typically minutes to hours. During that window, attackers post fake token contract addresses, fraudulent “airdrop” links, or “send X to receive 2X” scam posts. In 2023, a 45-minute breach of KuCoin’s Twitter account resulted in over $22,000 in losses before the account was recovered.
Crypto audiences are primed to act fast. Airdrop announcements, early access links, and time-sensitive deals are a normal part of crypto culture. Followers of official accounts are conditioned to act quickly on new posts — exactly the behavior attackers exploit.
According to Chainalysis’s 2025 mid-year crime report, over $2.17 billion was stolen from cryptocurrency services in the first half of 2025 alone — surpassing the entirety of 2024. Social engineering and account takeovers represented a growing share of these incidents.
How Attackers Compromise Crypto Social Accounts
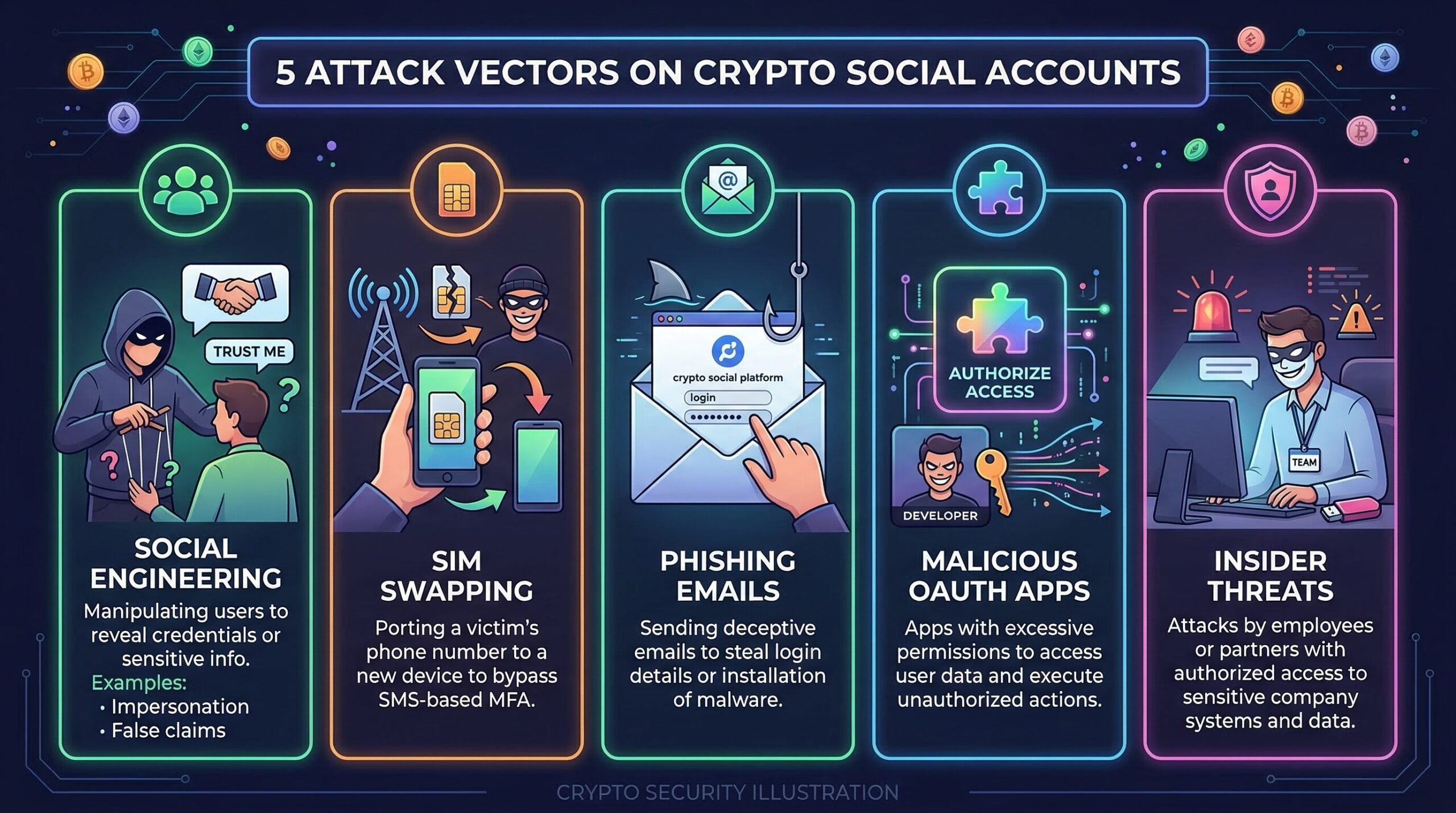
Understanding how attacks succeed is the first step to preventing them. There are several primary attack vectors documented in real-world crypto account breaches.
1. Social Engineering and Phishing
Social engineering — manipulating humans into revealing credentials or granting access — is the most common attack vector for social media takeovers. It requires no technical expertise to execute and bypasses even sophisticated technical security measures.
A typical social engineering attack targeting a crypto project’s social media manager might unfold like this: the attacker researches the target on LinkedIn, identifying the person who manages the project’s social accounts. They craft a convincing email appearing to come from Twitter’s support team, citing a “policy violation” or “verification issue” that requires immediate action. The email contains a link to a near-perfect clone of Twitter’s login page. The victim enters their credentials, which are captured by the attacker. If the victim also enters their 2FA code, the attacker uses it immediately to log in and initiate an account transfer before the code expires.
More sophisticated variants include attacks on third-party tools. Many crypto projects use social media management platforms (Hootsuite, Buffer, Sprout Social) or scheduling tools that have OAuth access to their accounts. Compromising the management tool grants access to every connected account. In Robinhood’s January 2023 breach, attackers posted a scam token from Robinhood’s Twitter, Instagram, and Facebook simultaneously — suggesting they had breached a shared social management tool rather than each platform individually.
2. SIM Swapping
SIM swapping is a type of social engineering attack targeting mobile carriers. The attacker contacts the victim’s mobile carrier, impersonating the victim and convincing the carrier to transfer the phone number to a new SIM card the attacker controls. Once successful, the attacker receives all SMS messages to that number — including 2FA codes for email, social media, and exchange accounts.
SIM swap attacks are particularly dangerous because they can bypass SMS-based two-factor authentication entirely. The defense is to remove phone numbers from account recovery options wherever possible and switch to authenticator app or hardware key-based 2FA.
3. Compromised Third-Party API Keys
Social media platforms provide API access for automated tools — bots, scheduling services, analytics platforms. These tools authenticate using API keys or OAuth tokens. If an attacker obtains a valid API key (through phishing a developer, breaching a third-party tool’s servers, or finding exposed keys in a public code repository), they can post to the account without needing the account password or 2FA.
In 2024, multiple crypto project accounts were compromised via a compromised API key belonging to a shared third-party tool. The attack affected all projects using the tool simultaneously, demonstrating the supply chain risk of third-party integrations.
4. AI-Powered Deepfake and Impersonation Attacks
The threat landscape in 2026 has expanded significantly due to AI. Security researchers and platforms including CoolWallet’s 2026 security guide and Ledger’s crypto scam report identify AI-assisted social engineering as one of the most significant emerging threats.
AI tools now enable attackers to clone voices for convincing phone calls impersonating executives or IT staff. Deepfake video technology can generate realistic video of project founders instructing staff to take actions — for example, “transfer the private key” or “add this new admin to the account.” These attacks bypass psychological defenses that rely on “that doesn’t sound like them” — because now it does.
5. Insider Threats
Not all account compromises come from external attackers. Disgruntled team members, improperly offboarded contractors, or bribed insiders represent a persistent risk. In May 2025, Coinbase faced a social engineering incident where bad actors reportedly bribed insiders to leak user data. Insider threats are particularly difficult to detect and defend against through purely technical means.
Notable Real-World Crypto Social Account Hacks
Reviewing actual incidents provides concrete examples of attack methods and their consequences:
TRON’s X Account (May 2025)
In May 2025, TRON’s official X (Twitter) account was compromised through what was described as a social engineering attack targeting account credentials. Attackers posted a fraudulent contract address, directing followers to send funds to a wallet the attackers controlled. The incident highlighted how even major blockchain projects — TRON ranks among the top 20 by market cap — are vulnerable to social layer attacks that no amount of smart contract security auditing would prevent.
Mandiant’s X Account (January 2024)
Mandiant, one of the world’s leading cybersecurity companies, had its own X account hacked for over six hours. Attackers renamed the account to impersonate Phantom crypto wallet and posted links to a fraudulent airdrop scam. The breach occurred despite Mandiant having 2FA enabled — suggesting the attackers either bypassed 2FA or exploited an account recovery mechanism. The incident is particularly notable because it victimized a cybersecurity professional organization, demonstrating that no organization is immune.
KuCoin’s Twitter Hack (April 2023)
KuCoin’s Twitter account was breached and used to post a fake giveaway. Within 45 minutes, followers who clicked the fraudulent link lost over $22,000 to the scam. KuCoin later reimbursed affected users and strengthened security protocols. This incident demonstrates both the speed at which damage occurs and the financial precedent of exchanges bearing responsibility for compromised official accounts.
Robinhood Multi-Platform Breach (January 2023)
Attackers compromised Robinhood’s Twitter, Instagram, and Facebook accounts simultaneously, posting a fake token called “$RBH” and directing users to purchase it. The simultaneous multi-platform compromise strongly suggests attackers had access to a social media management tool with cross-platform authorization rather than individually attacking each account. Robinhood recovered the accounts within hours.
The $HACKED Pump-and-Dump (September 2024)
A wave of major X account hacks in September 2024 was used to promote the Solana token “$HACKED.” Attackers compromised multiple high-profile verified accounts simultaneously and used them to post coordinated content about the token, driving a brief pump before dumping. The incident demonstrated the evolution of attack objectives: from simply posting fraudulent links to executing coordinated pump-and-dump schemes using compromised audiences as “social proof.”
Platform-Specific Vulnerabilities
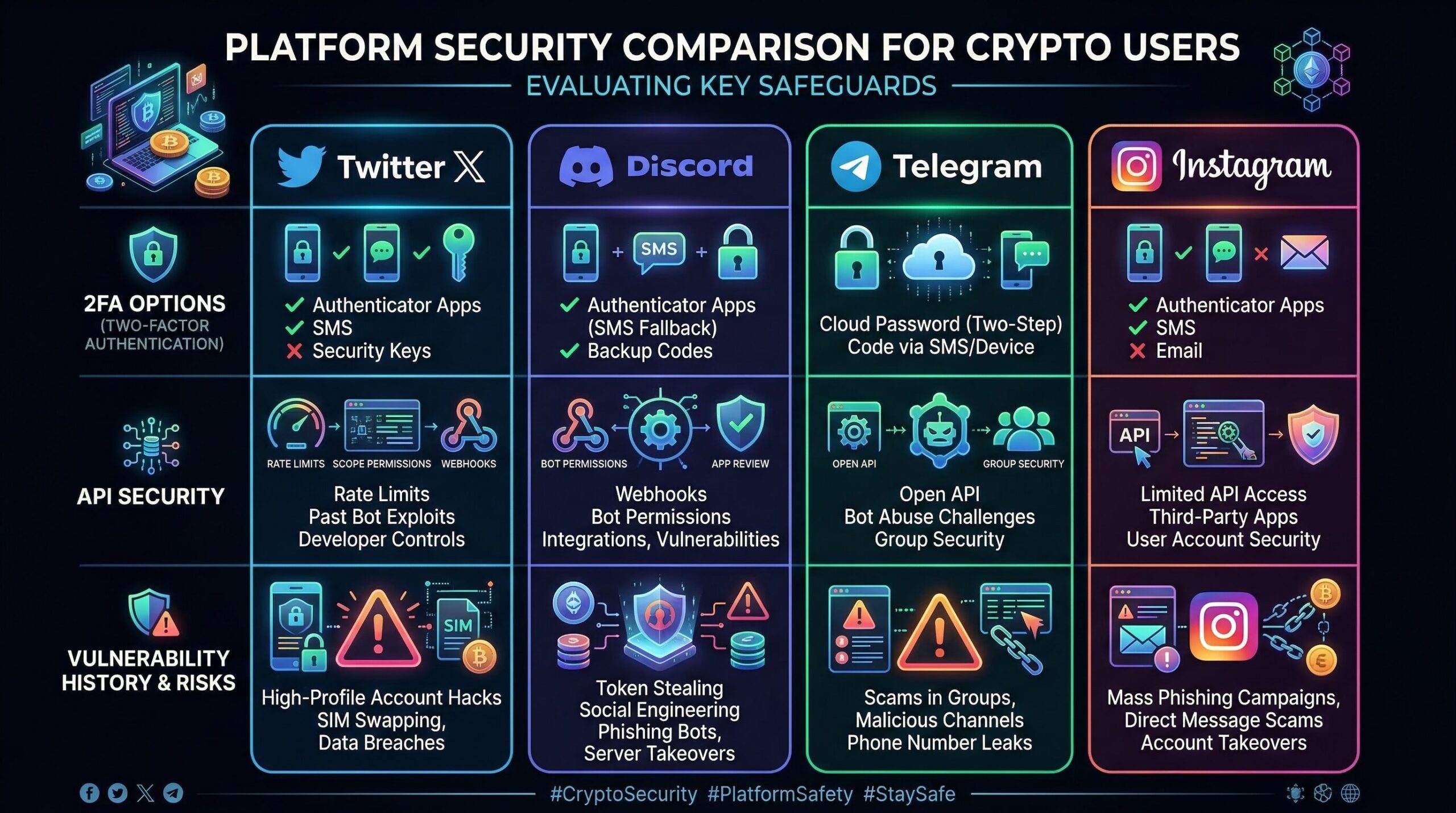
X (Twitter)
X is ground zero for crypto social media attacks. The platform’s real-time nature, verified account checkmarks (which can be purchased or transferred), and the culture of acting on breaking news create an environment where a compromised account can cause maximum damage in minimum time.
X’s security vulnerabilities have included high-profile data breaches: in 2025, a dataset containing over 200 million claimed X user records — including usernames, email addresses, and profile details — was published on hacker forums. While passwords were not included, email addresses extracted from such leaks enable targeted phishing campaigns against account holders.
X offers hardware security key support and strong 2FA options, but many users rely on less secure SMS-based 2FA. X’s account recovery processes have historically been vulnerable to social engineering by sophisticated attackers who can convince support staff of false ownership claims.
Discord
Discord is the primary community platform for most crypto projects and is a particularly attractive target. Discord compromises typically target server administrators or team members with elevated permissions. A compromised admin account can post malicious links pinned to all channels, DM all server members with phishing content, or transfer server ownership to the attacker.
A common Discord attack pattern involves a malicious bot invite or a webhook exploit that enables an attacker to post as if they were the project’s official account. In 2023 and 2024, dozens of NFT and DeFi project Discord servers were compromised through admin account phishing, with attackers posting fake “exclusive mint” links that drained wallets.
Telegram
Telegram channels and groups are widely used for crypto project communications and are a significant attack vector. Fake Telegram groups impersonating official project channels are extremely common — attackers create channels with near-identical names and manually add project followers, then post fraudulent information. Official project Telegram admins are targeted with phishing and social engineering for account takeovers.
Telegram’s phone number-based account system means SIM swapping can directly compromise Telegram accounts. Additionally, Telegram’s relatively limited moderation tools compared to other platforms make it difficult to quickly remove compromised content.
How to Protect Your Crypto Social Media Accounts: Complete Security Checklist
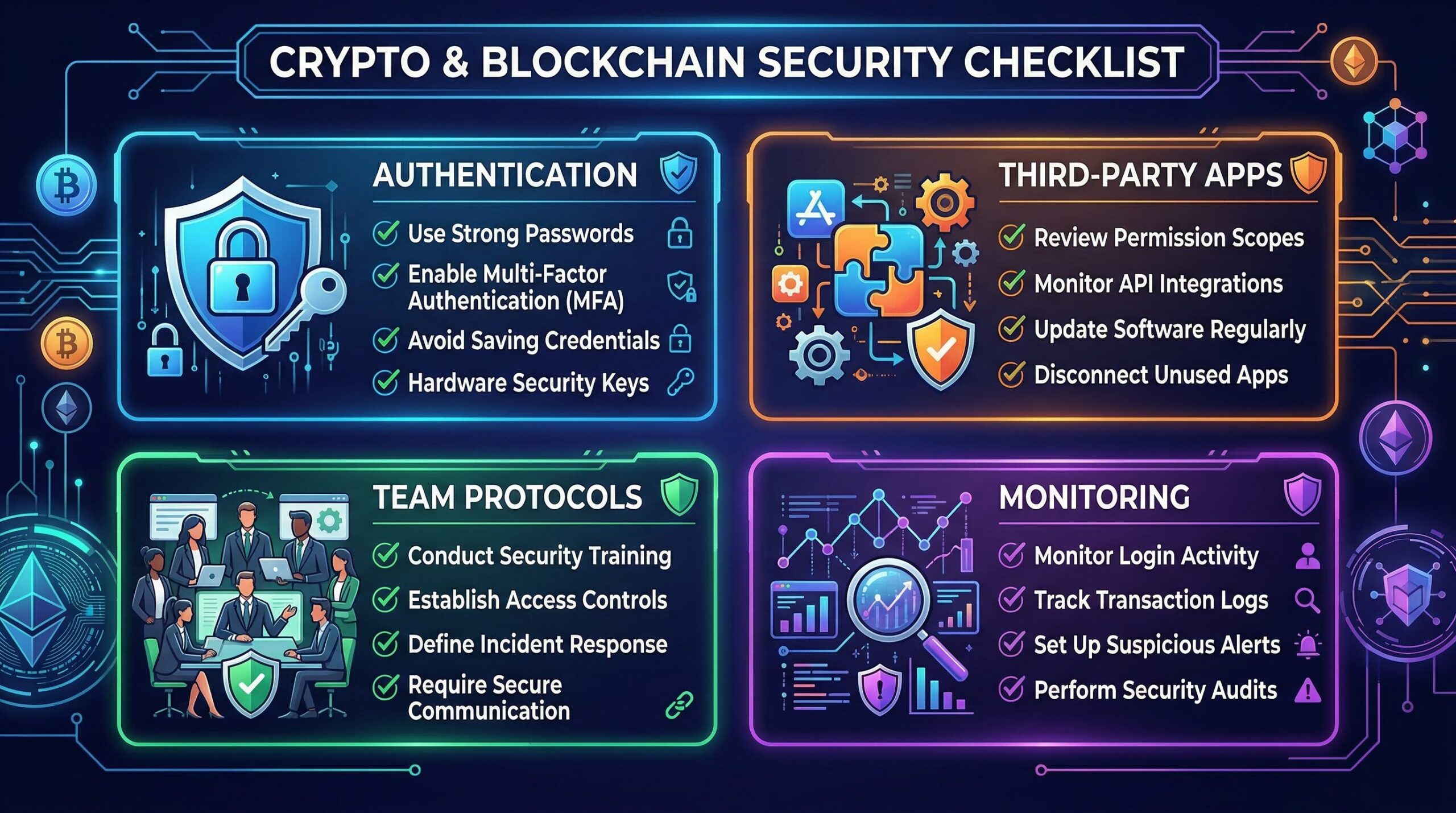
Authentication and Access Control
1. Use hardware security keys for all critical accounts. Hardware security keys (FIDO2/WebAuthn standard, such as YubiKey) are the gold standard for 2FA and are immune to phishing. Unlike SMS codes or authenticator apps, a hardware key physically cannot be used on a fake website — the cryptographic handshake only succeeds on the legitimate domain. Require hardware keys for all team members with social account access.
2. Remove SMS/phone number from all account recovery options. SMS-based 2FA is vulnerable to SIM swapping. Go through each platform’s security settings and replace SMS authentication with an authenticator app (Google Authenticator, Authy) or hardware key. Remove your phone number from account recovery wherever possible.
3. Use a dedicated email address for each social platform. Do not use your primary business or personal email as the account email for important social accounts. Create unique email addresses with strong, unique passwords for each platform, using an email provider with hardware key 2FA (Gmail, Proton Mail).
4. Enable all available login verification features. Most platforms offer login notifications — enable alerts for every new login so unauthorized access is detected immediately. On X, enable “two-factor authentication app” or “security key” under Security settings and disable SMS authentication.
5. Implement strict role separation. Not every team member needs admin access to social accounts. Implement minimum-privilege access: only those who genuinely need to post or manage accounts should have credentials. Use the platform’s team/page management features (where available) so individuals authenticate with their own accounts rather than sharing a master password.
Third-Party Tool Security
6. Audit all third-party app connections immediately. Go to each platform’s connected apps settings and review every authorized application. Revoke access for any app that is no longer in use, any app you don’t recognize, or any app that requests more permissions than necessary. Do this audit quarterly at minimum.
7. Treat API keys as passwords. API keys grant posting access without requiring a password. Store them in a secure password manager, never in plaintext files or code repositories. Rotate API keys regularly, especially when team members with access leave. Use platform-provided API key scoping to limit what each key can do (e.g., read-only vs. post access).
8. Vet third-party tools rigorously before connecting. Every social media management tool, scheduling platform, and analytics service you connect to your accounts represents a potential attack surface. Research the security practices of any tool before granting OAuth access. Prefer tools with SOC 2 certification, explicit security policies, and proven track records.
Team Operations and Human Factors
9. Implement an offboarding checklist that includes social account access revocation. Employee departures — even amicable ones — must trigger immediate credential rotation and access revocation. The window between an employee’s last day and credential revocation is an insider threat window. Make social account access revocation a mandatory step in every offboarding procedure.
10. Train all team members on social engineering tactics. Every person with any connection to your social accounts — posting, management, or even just knowledge of credentials — should receive regular security training. Key topics: how to identify phishing emails, what legitimate platform support requests look like, and the importance of never sharing credentials over any channel, even seemingly internal ones.
11. Establish a verification protocol for unusual requests. Create a team policy: any request involving account credentials, 2FA codes, or access changes must be verified through a pre-established out-of-band channel (e.g., a direct video call, not an email or Slack message). A request to “quickly share the password to update something” should trigger mandatory verification, not compliance.
12. Never reuse passwords across any accounts. Use a password manager (1Password, Bitwarden) to generate and store unique, complex passwords for every account. Password reuse means a credential breach on one platform compromises all others using the same password.
Incident Response Preparation
13. Prepare an incident response plan before you need it. Document the steps to be taken if an account is compromised: who is responsible for what action, which platform contact numbers and forms to use, how to communicate with your community during the incident, and who has authority to make public statements. Having this documented prevents panicked, uncoordinated responses during time-critical breaches.
14. Know your platform’s account recovery options in advance. Most platforms have emergency account recovery processes, but they take time. Understand the process for X, Discord, Telegram, and any other platform you use before you need it. Some platforms have dedicated enterprise support lines that provide faster response — worth considering for large-community projects.
15. Prepare a community communication template. Draft a “we’ve been compromised” message that can be sent through alternative channels (your website, email list, secondary accounts) within minutes of discovering a breach. Rapid, clear communication helps followers avoid the scam and reduces total financial damage.
Ongoing Monitoring
16. Set up alerts for your project name and official accounts. Use monitoring tools to receive immediate notifications if your project name appears in unusual contexts — for example, if a new account with your project’s name but slight variations suddenly gains followers, or if your official account posts content outside normal hours.
17. Monitor connected app permissions monthly. Make a calendar reminder to review all third-party app connections across all platforms monthly. Revoke any apps that have been connected for unknown reasons or that you did not explicitly authorize.

What to Do If Your Account Is Compromised
Speed is critical. The longer a compromised account remains active, the more damage occurs. Follow these steps in order:
Step 1: Attempt immediate account recovery. On most platforms, triggering “forgot password” and using your secure email can initiate recovery. If you can regain access, immediately change the password, revoke all sessions, rotate 2FA, and audit connected apps.
Step 2: Contact platform support immediately. File an emergency account compromise report with the platform. Have your account verification documentation ready (government ID for personal accounts, business registration for organizational accounts). Describe the situation clearly: “My account was compromised and is currently being used to post fraudulent cryptocurrency content.”
Step 3: Alert your community through alternative channels. While recovery is in progress, immediately post on any uncompromised channels — your website, secondary accounts, email list — warning followers that your account has been compromised and any links posted in the last [timeframe] are fraudulent. Do not click any links. This step can prevent substantial financial harm to your community.
Step 4: Document everything. Screenshot all fraudulent posts, note timestamps, capture any wallet addresses mentioned in scam posts. This documentation is necessary for law enforcement reports and platform recovery requests.
Step 5: Conduct a post-incident audit. Once the account is recovered, audit how the breach occurred. Was it a phishing attack on a team member? A compromised third-party tool? An offboarded employee? The root cause must be identified and addressed to prevent recurrence.
Red Flags: Identifying a Compromised Account
If you follow a crypto project on X, Discord, or Telegram, knowing how to identify a potentially compromised account can protect you from significant financial loss. Key warning signs:
- Unusual posting time: A post appearing at 3 AM local time from an account that normally posts during business hours
- New token or contract address posted without advance notice: Legitimate projects rarely launch tokens without prior community discussion; sudden “surprise” token announcements with urgency are almost always scams
- Requests to send crypto to receive more crypto: No legitimate project or individual does this; it is always a scam, always
- “Limited time” giveaways requiring wallet connection: Connecting your wallet to an unknown contract can drain all your assets
- Account name or handle changes: Attackers sometimes rename accounts before posting scams, then rename them back; check account handles carefully
- Links to domains that are not the official project domain: If a post from a project’s Twitter directs you to a URL that isn’t the project’s known domain, treat it as compromised
When in doubt, check the project’s website directly (not from any posted link — type it manually) or look for announcements from other uncompromised channels before taking any action.
The Bigger Picture: Social Engineering in 2026
The 2026 threat environment is more sophisticated than previous years. On-chain security analysts predict that while 2026 may see improvements in smart contract and protocol security, attackers will increasingly pivot to complex social engineering and AI-assisted fraud — precisely because these attack vectors are harder to automate defenses against.
AI capabilities including voice cloning, deepfake video generation, and highly personalized phishing content mean that the social engineering attacks of 2026 are substantially more convincing than those of even two years ago. A video call from someone who looks and sounds like your project’s founder asking you to take an action — and that video call is AI-generated — represents a threat that requires procedural defenses, not just technical ones.
The core defense principles remain unchanged: verify through established channels, apply minimum-privilege access, never share credentials under pressure, and audit third-party access regularly. But the context in which these principles must be applied is increasingly adversarial and sophisticated.
Conclusion: Security Is a Continuous Practice
Social media account security is not a one-time configuration. It requires ongoing maintenance: regular audits of connected apps, consistent training of everyone with account access, disciplined offboarding procedures, and practiced incident response.
For crypto projects, the stakes are particularly high. Your official accounts carry the trust of your entire community — followers who act on your posts and announcements, often with real financial consequences. That trust is extremely valuable to attackers and extremely fragile once broken. A single successful account compromise can cause lasting reputational damage that no security patch can fully repair.
Implement the security measures in this guide today, before you need them. The cost of preventive security is a fraction of the cost of responding to a breach.
Last updated: March 2026. Specific platform security settings may change as platforms update their interfaces. Always refer to each platform’s current security documentation for the most up-to-date instructions.
